Rabu, 30 Julai 2008
Some Google Tricks
Hand type the following prefixes and note their utility:
link:url Shows other pages with links to that url.
related:url same as "what's related" on serps.
site:domain restricts search results to the given domain.
allinurl: shows only pages with all terms in the url.
inurl: like allinurl, but only for the next query word.
allintitle: shows only results with terms in title.
intitle: similar to allintitle, but only for the next word. "intitle:webmasterworld google" finds only pages with webmasterworld in the title, and google anywhere on the page.
cache:url will show the Google version of the passed url.
info:url will show a page containing links to related searches, backlinks, and pages containing the url. This is the same as typing the url into the search box.
spell: will spell check your query and search for it.
stocks: will lookup the search query in a stock index.
filetype: will restrict searches to that filetype. "-filetype:doc" to remove Microsoft word files.
daterange: is supported in Julian date format only. 2452384 is an example of a Julian date.
maps: If you enter a street address, a link to Yahoo Maps and to MapBlast will be presented.
phone: enter anything that looks like a phone number to have a name and address displayed. Same is true for something that looks like an address (include a name and zip code)
site:www.somesite.net "+www.somesite.+net"
(tells you how many pages of your site are indexed by google)
allintext: searches only within text of pages, but not in the links or page title
allinlinks: searches only within links, not text or title
I hope there is something new in here for you and maybe this infos will be helpfull for ya.
how to search google for RAPIDSHARE links
Paste this into the google search window (not the adress bar):
site:rapidshare.de -filetype:zip OR rar daterange:2453402-2453412
* this searches the site rapidshare.de for any file that is rar or zip, and
has been indexed between 1-11 February.
dvd site:rapidshare.de -filetype:zip OR rar daterange:2453402-2453412
* this is the same search but it specifically searches for "dvd" with the same
search criteria, so any app posted with the word dvd in it will be found.
There are mainly three criteria to keep in mind when doing this search.
1. site: your site of choice to search
2. filetype: filetypes you wanna search,if you put a "OR" after the first
filetype you can add more.
3. daterange: (start date-enddate)
* this uses the "julian calendar", converter can be found here:
Code:
http://aa.usno.navy.mil/data/docs/JulianDate.html
Converting HDD to NTFS
The recommended option
There are a number of features in Windows XP that will only work if the NTFS file system is present, which is why it’s suggested you make use of it. File and folder permissions, encryption and privacy options are just some of those you’ll be able to access. In particular, those of you who have set up user accounts will find NTFS invaluable. For instance, if you continue to use FAT or FAT32 anyone with physical access to the drive will be able to access the files and folders that are stored there. However, with NTFS you’ll be able to use a level of encryption (Professional Edition only) that will enable you to protect your data.
You’ll also find NTFS more reliable in that it’s more able to recover from disk errors than its FAT or FAT32 counterparts. A log of all disk activity is kept so should a crash occur, Windows XP can use this information to repair the file system when your PC boots up again. To find out what file system you’re using, open My Computer, right-click your main hard drive and choose Properties. Take a look at the General tab to see confirmation of the file system that’s in use.
Convert now
You can use the convert tool in Windows XP to change the file system on your hard disk from FAT or FAT32 to NTFS. The whole process is safe and your existing data won’t be destroyed. To begin, click Start -> Run, type cmd and press [Return]. At the command prompt type convert c: /fs:ntfs and press [Return] (where ‘c’ is the letter of the drive you’re converting). When you try and run the convert utility, it’s likely that Windows XP will be using your paging file so the process won’t be completed immediately. Therefore, you’ll see a brief message on screen informing you that the conversion will take place instead the next time Windows starts up. Having restarted, the Check Disk utility will run, the conversion will be performed automatically and you may find that your PC will reboot twice more.
The benefits
With your drive now running NTFS, it’s time to take advantage of the new options that are available. Having created a number of different user accounts you can now control the level of access that’s granted to individual users. For example, there are going to be certain files and folders that you’ll want some users to be able to access but not others. If you have Windows XP Professional Edition you can do this immediately.
Right-click any file or folder, choose Properties and select the Security tab. A dialog will be displayed showing the names of all your users. Alongside will be two columns which enable you to select levels of access for each of them, the permissions include Full Control, Modify, Read and Write. You can then check the appropriate box to determine whether or not to Allow or Deny a particular permission. For Windows XP Home Edition users, the Security tab won’t be immediately available. To access this option you’ll need to restart your PC, pressing [F8] until a menu appears. Next select Safe Mode and wait for Windows XP to start up. You can then set your options in the same way.
Another feature is NTFS compression. It’s quick and seamless as your file or folder is decompressed automatically when you access it. (Don’t confuse this with a Zip compression utility where the files need to be extracted before they can be accessed.) Although you may have used NTFS compression on a file or folder, there’s no way of telling just by looking at it. To remedy this, open My Computer, click Tools -> Folder Options and select the View tab. Under Advanced settings, scroll down and check the option ‘Show encrypted or compressed NTFS files in color’, then click Apply and OK. Take a look at your compressed items in My Computer and you’ll see the text label has changed from black to blue. Something else that’s exclusive to Professional Edition users is the Encrypting File System (EFS). You can use this to protect your important data so that no one else can read it. Your encrypted files and folders will only be accessible when you have logged into your user account successfully.
Ahad, 22 Jun 2008
How to build System Information Usefull?
To make a system information that usefull you must look for what the functional the application which will build and what the function will be helpfull. This talk how about make application which can operational by operator system and how much that application can help they works. Whats do you must know?
- Functional Requirements. The functional requirements is statements of services the system should provide, how the system should react to particular inputs and how the system should behave in particular situation. The example: the system shall provide appropriate viewer for the user to read the documentation in the document store.
- Non-functional requirements, its the constraint on the service or functions offered by system such as timing constraints, constraints development process, standard and etc.
- User Requirements is statements in natural language plus diagram of the service the system provide and all its constraints. Written for costumers or operators system. (such as documentation, user manual)
- System Reuquirements is a structured documentation, detailed description of the system's functions, service and operational constraints. Defines what should be implemented so may be part of a contract between client and contractor
- Interface Specification, most system must operate with other system and the operating interfaces must be specified as part of the requirements Three types of interface may have to be defined: procedural interface, data structurees that are exchanged, data representation.
- The Software Requirements Documents is the official statement of what is required of the system developers. Should include both a definition of user requirements and a specification of the system requirements. It is a not a design document. As far as possible, it should set of what the system should do rather than how it should do it.
- The Library System is a library that provide a single interface to a number of databases of article in different libraries
- Goal and Requirement are helpful to developers as they convey the intentions of the system users. such as a general intention of the user such as ease of use by experienced controlled and should be organised in such a way that user errors are minimised
In the written user manual or documentation for customer or user, we must use natural language in order they will understand, ussually we meet some problem with natural language, such as
- Lack of clarity. Precision is difficult without making the document, difficult to read
- Requirement confusion. Functional and non-functional requirement trend to be mixed-up
- Requirement amalgamation. Several different requirements may be expressed together.
4 Point tips for writting requirements
- Use language in consistent way. Use shall for mandatory requirements, should for desirable requirements
- Invent a standard format and use its for all requirements
- Use Text highlighting to identity key parts of the requirements
- Avoid the use of computer jargon
- Ambiguity
The readers and writers of the requirement must interpret thesame words in the same way. NL is naturally ambiguous so this is very difficult. - Over-flexibility
The same thing may be said in a number of different ways in thespecification. - Lack of modularisation
NL structures are inadequate to structure system requirements.
Graphical models
Graphical models are most useful when you need to show how state changes or where you need to describe a
sequence of actions.
Key points
- Requirements set out what the system should do and define constraints on its operation and implementation
- Functional requirements set out services the system should provide.
- Non-functional requirements constrain the system being developed or the development process.
- User requirements are high-level statements of what the system should do. User requirements should be written using natural language, tables and diagrams.
- System requirements are intended to communicate the functions that the system should provide.
- A software requirements document is an agreed statement of the system requirements.
- The IEEE standard is a useful starting point for defining more detailed specific requirements standards.
Selasa, 17 Jun 2008
Temperature Monitoring Program in VB 6.0
Membuat Program Chatting Sendiri di VB 6
Option Explicit
Private Sub Form_Load()
'inisialisasi sock untuk membuka port,
'pertama cek apakah socket keadaan terbuka
'jika iya maka socket ditutup, kemudian
'buka port 1234 untuk berkomunikasi
If Winsock1.State = 2 Then Winsock1.Close
Winsock1.LocalPort = "1234"
Winsock1.Listen
End Sub
________________________________________________________________________
'tombol perintah untuk koneksi ke komputer yang lain
'di alamat 192.168.100.2
'dengan port 1234
Private Sub Command2_Click()
On Error GoTo out
Winsock2.Close
Winsock2.Connect "192.168.100.2",1234
Exit Sub
out:
MsgBox "Gagal kirim pesan!", vbCritical
End Sub
________________________________________________________________________
'tombol perintah untuk mengirim data kepada socket
'yang terhubung dengan port yang 'dibuka oleh windsock1 yaitu port 1234
Private Sub Command1_Click()
On Error GoTo out
Winsock1.SendData Text1.Text
Exit Sub
out:
MsgBox "Gagal kirim pesan!", vbCritical
End Sub
________________________________________________________________________
'event pada socket jika terjadi permintaan koneksi
Private Sub Winsock2_ConnectionRequest(ByVal requestID As Long)
Winsock2.Close 'tutup socket
Winsock2.Accept requestID 'kemudian baru terima request id
End Sub
________________________________________________________________________
'event pada socket jika terjadi penerimaan data
Private Sub Winsock2_DataArrival(ByVal bytesTotal As Long)
Dim dataz$
'ambil data yang diterima disimpan pada variable dataz
Winsock2.GetData dataz
'tampilkan hasil data yang telah diterima pada textbox
Text2.Text = Text2.Text + vbCrLf + CStr(Time) + ">>" + dataz
End Sub
________________________________________________________________________
'event pada socket jika terjadi permintaan koneksi
Private Sub Winsock1_ConnectionRequest(ByVal requestID As Long)
Winsock1.Close 'tutup koneksi
Winsock1.Accept requestID 'kemudian baru terima request id
End Sub
________________________________________________________________________
'event pada socket jika terjadi penerimaan data
Private Sub Winsock1_DataArrival(ByVal bytesTotal As Long)
Dim dataz$
'ambil data yang diterima disimpan pada variable dataz
Winsock1.GetData dataz
'tampilkan hasil data yang telah diterima pada textbox
Text2.Text = Text2.Text + vbCrLf + CStr(Time) + ">>" + dataz
End Sub
________________________________________________________________________
Private Sub Form_QueryUnload(Cancel As Integer, UnloadMode As Integer)
Winsock1.Close
End Sub
________________________________________________________________________
Tentunya penggunaan satu socket hanya untuk satu koneksi, jadi kalo kamu pengen dapat berkomunikasi lebih dari dua komputer, kamu bisa membuat array untuk object winsock kamu. Caranya ambil Winsock 1 saja letakkan di form, kemudian pada properti winsock di bagian index isikan 0. Kemudian pada setiap kamu mau melakukan komunikasi kamu harus meload object tersebut. Misal mau melakukan koneksi pada komputer 1 maka lakukan perintah
.....
Load Winsock(1)
Winsock(1).Connect "193.168.100.2",1234
dan lakukan hal yang sama jika ingin berkomunikasi dengan komputer yang lain. Catatan, jika koneksi telah berakhir hendaklah mengunload object yang tidak terpakai, dengan tambahan pula ada baiknya sebuah variable yang mencatat objek index apa saja yang terpakai dan yang tidak terpakai. Misalkan dengan menggunakan variabel class Collection. Ya.. itu saja, semoga bisa membantu bagi kamu-kamu yang pengen buat aplikasi chatting sendiri ala kamu sendiri. Selamat mencoba.
Get Monolopy Bandwidth With Mozilla Firefox
network.http.pipelining.maxrequests set value 64,
network.http.proxy.pipelining set it true
network.proxy.share_proxy_settings set its value false, after that all you make one entry lists with name nglayout.initialpaint.delay and set its value 0, its type data is integer. And its you can improve your browser with used proxy switcher, you can download it at https://addons.mozilla.org/extensions/moreinfo.php?applicationfiltered=firefox&id=125 and install that plugin. Then you restart your Mozilla Firefox application. Happy fun.
Isnin, 16 Jun 2008
Ber Yahoo Messenger di hape...
Terus untuk aplikasi symbian, kamu bisa gunain aplikasi YM dari Lonelycatgames, nama aplikasinya adalah slick. Nah.. gunain dech google search buat bantu kamu cari program itu.. program itu secara gratis tersebar diinternet koq. Ok.. begitu aja.. semoga berhasil berchatting ria ala YM di mobile phone kamu.
Lets know about RootKit
Type of rooktis are five: firmware, virtualized, library, kernel and application level kits.
How to detected them???
To detected the rootkits, its can be used bys siganture or heuristics based antivirus program. Usually they can be detected by scan all of modules from any programs running or its running in invisible window mode.
Articel source :http://en.wikipedia.org/wiki/Rootkit
How to Our site survive in list SE
How to our site survive in list SE?? Its the one of many questions, well.. the widening reach of the Internet in our daily lives, has opened many doors of opportunities for many individuals today. The Worldwide web has created new terms, references, and a wider blend of career opportunities, and methods to earn more profits, as well as devising new marketing and sales strategies. The art of search engine optimization is a direct result of such new developments. For those who see themselves as Internet-savvy individuals and possess a much deeper insight of how the Internet moves and thinks, then they can earn themselves a great career through this novel method.
Search engine optimization refers to the kind of service which helps to increase the exposure of a Business or organization's Web site or Web pages. Attaining adequate exposure could mean a lot of good things for different organizations, firms, groups or industries who long for a wider reach with online readers and consumers.
Create An Opening Paragraph That Effectively Describes Your Page Content
It's a fact that most established search engines love content, however they are especially fond of the first 25 words on each page. By providing an opening paragraph that perfectly or appropriately describes the content of the rest of the page , or the site itself, you would be able to include your vital keyword phrases in this important area.
When users first arrive in a Web page, the first thing that they will need to know is whether that exact offers the information they're looking for. A logical step in finding out, is to scan through the first paragraph, which, if it appropriately and comprehensively describes the page content, should be very helpful.
Remember To Utilize Meaningful Page Titles
A meaningful page title helps your Web site's visitors to get a full understanding of where they are,both within the site, and on the Internet as a whole. As you probably know already, the page title is the first thing that loads up, generally quite a few seconds before the actual content, therefore a descriptive, keyword-rich page title can truly help in effective user orientation to your site.
If you don't know that much about SEO yet, you'll find out that most search engines put a premium on the page title than on any other of the page's attributes. If the title comprehensively describes the content of that page, the legitimate search engines should be able to accurately discern what that page is actually about.
Make It A Habit To Provide High-Quality Content
Although this may sound like an off-beat characteristic of a search-optimized Web site, it's actually a very important one. Most standard search engines, in addition to page content, verify at the number of links that are pointing into the Web pages.
Generally, the more inbound links a Web site has, the higher will the site's search rankings appear. In writing and providing unique, interesting, fresh and regularly updated content on your Web site, this will make other Web masters want to link to your site. By doing that, it would also be able to provide extra value to their site, and to their visitors as well.
Comprehensively optimizing your online firm's Web site for both search engines and online visitors, shouldn't be seen as a mere trade-off., because while there is a significant overlap between the tasks required to achieve these two vital objectives, this overlap can be used to your advantage. It shouldn't be too challenging to create a Web site that users can easily locate via the search engines, and completely use once they reach it.
| Vanessa A. Doctor from Jump2Top - SEO Company Article Source: http://EzineArticles.com/?expert=Vanessa_A._Doctor | |
Lets Know About SEO
Basically it is all about to improving your website so that it appears near the top of the search results for your chosen keywords.
In recent years it has become very big business and a lot of people have made a lot of money either by optimising their own sites or through the work they have done in optimising other people's websites.
Like a lot of profitable industries, the SEO market place has seen (and continues to see) it's fair share of people jumping on the bandwagon and all claiming to be SEO experts.
There are lots of people claiming its highly technical or highly secretive. You'll probably hear people claim that they have cracked the Google Algorithm. I doubt it!
For me it's quite clear that for the search engines to survive they need to serve up highly relevant sites that match the searches their customers are doing. That way, their customers will stay with them. It's the model that Google uses. They focus completely on giving users of its search engine highly relevant and high quality websites. Yahoo has been quick to follow Google's lead.
So a lot of SEO techniques are based around the idea of making sure the search engines can see that your site is relevant for your chosen keywords and is high quality.
A word of caution, avoid what are known as Black Hat SEO techniques. These are techniques that try to trick the search engines into giving a website a higher placement in the search engines than the website deserves. They are usually based on some exploitable flaw in the rules that the search engines use to work out how relevant your website is for the keywords you are targeting. The problem with these techniques is that not only do they usually promote websites that give a poor user experience but also their high position in the search engines is usually short lived once the flaw they are exploiting is fixed.
If you want to try some ethical and successful SEO techniques then there are a few professionals that are worth listening to. Aaron Wall and Dan Thies are names I would put into Google to find out more.
Mike Seddon is the founder of KKSmarts. Their site contains many free guides including their Free SEO Training Online Course.Article Source: http://EzineArticles.com/?expert=Mike_Seddon
Khamis, 12 Jun 2008
How to set wifi ad hoc? (peer to peer)
1. Connected to Access Point Mode
2. Connected peer-to-peer, where the device is same platform that support ad hoc mode
at Windows XP:
First, at Wireless Network Connection
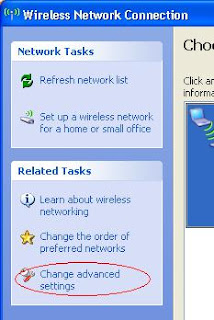
Select change advance settings, then select tab Wireless Networks - Click button advanced
then show new dialog Advanced.
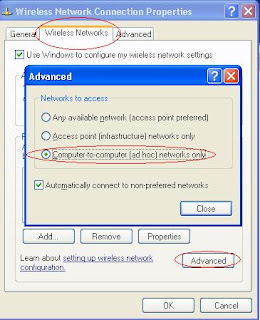
Select optional Computer-to-Computer (ad hoc) network only at Network to access frame
Then click close - > OK
After that you do all, then you must setting at Wireless Network Connection Properties to add.. name connection.
 Add a name for your name connection wi-fi in order other computer wi-fi can detect your wi-fi name.
Add a name for your name connection wi-fi in order other computer wi-fi can detect your wi-fi name.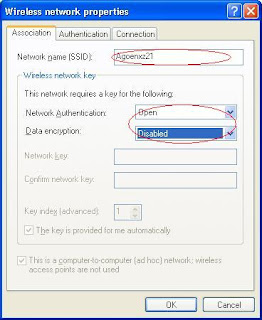 Look at picture side. Setting Network Authentication for Open and Data encryption can be disbled to make easy for connected. After that, the other computer set same too, and start for scan Wireless connection available. If this way success it will show at list the name wi-fi which have been setting. And it might could be connection to communication between two computers there.
Look at picture side. Setting Network Authentication for Open and Data encryption can be disbled to make easy for connected. After that, the other computer set same too, and start for scan Wireless connection available. If this way success it will show at list the name wi-fi which have been setting. And it might could be connection to communication between two computers there.How To Make Your Web Indexed By SE
- Create your links to your web address at page website which have been indexed by SE, or you can make some relations with your friend, some like you contact they all to visite your website or blog, or make your links website at they website. And you must frequently update your website content.
- Be sure your blog or website not at undercondition, not have a dead link at your page, your website make search engine friendly
- Submit manual your website address at this URL (FREE):
- Google: http://www.google.com/addurl.html
- Yahoo: http://search.yahoo.com/info/submit.html
- MSN: http://search.msn.com/docs/submit.aspx
Rabu, 11 Jun 2008
Make a simply personal antivirus with visual basic 6.0
Download at here:
http://rapidshare.com/files/121715745/FreeAVScr.rar.html
Create SpyVB with Visual Basic 6.0
http://rapidshare.com/files/121682416/vbspy.rar.html
Selasa, 10 Jun 2008
Step by Step Make Money Internet adsense
First, actually you must have one account for email address,
Second, you can make a website or blog. Its have some web hosting that provide website for you for free, other wise you can make it at blog, like blogger.com
third, you can join agent advertiser publisher like google adsense, adbrite, BidVertiser and more. You must have account one for publisher type not other.
Fourth, then you embeded your get code HTML adsense from your agent adsense to your website or blog which have been you create
Fiveth, do promotion for your web or blog to every one. You can try for several website that provide to help you promotion your website address.
sixth, do not click your adsense at your computer if adsense have available shows at your website or blok
seventh, you can try social engineering for appeal every body to visit your website. Like, you can give some tips or trick at forums and then give your link website for reason to get more detail
Hope fully this bits tips can help you for begin bussines internet marketing.
Isnin, 9 Jun 2008
10 Ways To Get New Product Ideas
2. Find out what's the current hot trend. You can find out what the new trends are by watching T.V, reading magazines and surfing the net. Just create a product that's related to the current hot trend.
3. Improve a product that is already on the market. You see products at home, in ads, at stores etc. Just take a product that's already out there and improve it.
4. Create a new niche for a current product. You can set yourself apart from your competition by creating a niche. Your product could be faster, bigger, smaller, or quicker than you competitor's product.
5. Add on to an existing product. You could package your current product with other related products. For example, you could package a football with a team jersey and football cards.
6. Reincarnate an older product. Maybe you have a book that's out of print and is no longer being sold. You could change the title, design a new front cover, and bring some of the old content up to date.
7. Ask your current customers. You could contact some of your existing customers by phone or e-mail and ask them what kind of new products they would like to see on the market.
8. Combine two or more products together to create a new one. For example, you could take a brief case and add a thermos compartment inside to keep a drink hot or cold.
9. Survey the people who visit your web site. You could post a survey or questionnaire on your web site. Ask visitors what kind of products they would like to see on the market.
10. You could create a new market for your existing product. For example, if you're selling plastic bottles to a pop company, you could turn around and sell those bottles to a fruit drink company
source:http://www.onlinegoldmoney.com/mod.php?mod=userpage&menu=118&page_id=15
How to keep viruses away from your computer.
I will some tips for you to solve its problems.
Step One
Always keep a updated version of your a anti-virus software. You may find free versions at on the internet. Use a search engine and type in free anti-virus software. Like a signature database.
Step Two
Recognize the symptoms of a virus. If you have any suspicions of a virus on you computer, run your anti-virus software;
Step Three
Let your virus software run daily. I usually have it automatically run when I start up the computer. Do not disable your software;
Step Four
Setting your anti-virus software to check all incoming downloads;
Step Five
Please Do not down load files from unknown sources.
source : http://www.ehow.com/how_2227619_keep-viruses-away-computer.html
Step 1
When your computer comes from the factory with it's default settings, it has been optimized to run properly. Over time, as you add files and software - and just as importantly, remove files and software - your computer gets farther and farther away from it's optimal settings. To put this in perspective, it would be like adding parts to your car, and then removing some other parts and then adding more parts after that. Finally, your car doesn't run very well anymore.
Step 2
More specifically, there are several primary areas that could be causing your computer to run slow. The most likely reason is that your registry has become corrupt and your system is essentially running in circles with its internal processing.
Step 3
The second most common problem is that you have too many programs running behind the scenes. In this case, we're not talking about the programs you know about that are running at the bottom of your task bar, such as Outlook Express or your internet browser window. But behind the scenes, there can be literally hundreds of programs of various sizes running in the background. These are eating up your computer's available processing capacity and can bring your system to a literal stand still.
Step 4
To determine if your system is in fact running slow because of problems in your registry, you will need to run a self diagnostic program such as Registry Patrol. This easy to use program will perform a deep scan on your computer and will report back on any issues or problems it finds for you at no charge - which means you can figure out what is wrong without having to buy anything in advance or pay a technician to essentially perform the same function.
Step 5
For more resources and additional information check the RESOURCES section at the bottom of this page.
source:http://www.ehow.com/how_2225155_speed-up-slow-computer.html
How to Convert a .pdf file to HTML or plain text
There is a feature in GMail that will convert Adobe PDF documents into HTML files. [In addition to PDF, it will convert any Microsoft Office document to HTML.] The very first thing to do is create a Gmail account if you don't already have one. This is free; go to Google and click on mail- register for an account.
Step 2
Next, compose an email message to yourself in Gmail.
Step 3
Attach your PDF file. You can attach several files simply by clicking on "Attach another File".
Step 4
Send it to yourself using your Gmail address. It will instantly appear in your Gmail account. Open it.
Step 5
Click View as HTML at the bottom of the message. [You can also click on plain text if you prefer then follow the same steps as the HTML instructions.]
Step 6
You can then save it as a document file by cutting and pasting into a new document. Save it with a new name in your documents files.
Then, you can cut and paste it wherever you want! Go ahead. Have fun.
Ads by Google
PDF Converter for MS Word
One-Click PDF Conversion to Word, Excel, HTML and more!
www.verypdf.com
Convert PDF to Doc Easily
ABBYY PDF Transformer – the most accurate PDF conversion tool
www.pdftransformer.com
Scan to PDF Software
Scan and create PDF. Full Demo. Barcode, OCR, Email, APIs, and more
www.scantopdf.co.uk
Print in PDF
Convert your documents to PDFs Free, Fast & Online
www.printinpdf.com
Tips and Tricks Free Internet
For CDMA F**r**e**N
- setting your browse, fill Manual Proxy 203.160.1.146, Port 554
- setting your modem fill “AT+CRM=1” without tanpa tanda kutip pada bagian Extra Initialization Commands.
- Now, you can do dial-up. username:m8 password:m8 dial: #777, then open your browser (recomended use firefox), if failed, try more.. disconnected and connected again
- Acces Point Name : 3mms
- at browse setting : DNS 1 : 208.67.229.229, DNS2: 208.67.227.227 or 6 digit last can be change
- dial up : username and passwors 3mms
- if you connected, to be sure you get IP Client 10.25.*.*
- do connect / disconnect until u get client IP 10.25.*.*
- recommended use firefox browser
- Acces Point Name 3gprs
- at your browser setting, fill Manual Proxy with Proxy from Emirat Arab dan Port 443 atau port 53
- Do dial up : username and passwors 3gprs
- Recommended use browser Opera 5 or older
- proxy 195.175.37.71 dan port 8080
- Dial up
- Recommended use browser Opera and used modem mobila symbian OS
For GMS IM****3
- APN : www.indosat-m3.net
- URL : wap.m3-access.com
- IP : 290.063.054.053 and port IP:9201
- Recommended use IE browser
How to SMS Gateway with Visual Basic 6.0
Hem.. do you ever think to do that?? its look greate, if you make applications more powerfull with feature sms gateway which integrated. Its.. some example source code VB 6.0, might its will give you some brightness about sms gateway with visual basic 6.0.
Note: its used some activex that you must regsvr32 first files them all. and its used database MSSQL 2000. You can download at here:
http://rapidshare.com/files/121091783/SMSGw.rar.html
Visual Basic
Although programs can be compiled into native code executables from version 5 onwards, they still require the presence of runtime libraries of approximately 2 MB in size. This runtime is included by default in Windows 2000 and later, but for earlier versions of Windows or Windows Vista, it must be distributed together with the executable.
Forms are created using drag and drop techniques. A tool is used to place controls (e.g., text boxes, buttons, etc.) on the form (window). Controls have attributes and event handlers associated with them. Default values are provided when the control is created, but may be changed by the programmer. Many attribute values can be modified during run time based on user actions or changes in the environment, providing a dynamic application. For example, code can be inserted into the form resize event handler to reposition a control so that it remains centered on the form, expands to fill up the form, etc. By inserting code into the event handler for a keypress in a text box, the program can automatically translate the case of the text being entered, or even prevent certain characters from being inserted.
Visual Basic can create executables (EXE files), ActiveX controls, DLL files, but is primarily used to develop Windows applications and to interface web database systems. Dialog boxes with less functionality (e.g., no maximize/minimize control) can be used to provide pop-up capabilities. Controls provide the basic functionality of the application, while programmers can insert additional logic within the appropriate event handlers. For example, a drop-down combination box will automatically display its list and allow the user to select any element. An event handler is called when an item is selected, which can then execute additional code created by the programmer to perform some action based on which element was selected, such as populating a related list.
Alternatively, a Visual Basic component can have no user interface, and instead provide ActiveX objects to other programs via Component Object Model (COM). This allows for server-side processing or an add-in module.
The language is garbage collected using reference counting, has a large library of utility objects, and has basic object oriented support. Since the more common components are included in the default project template, the programmer seldom needs to specify additional libraries. Unlike many other programming languages, Visual Basic is generally not case sensitive, although it will transform keywords into a standard case configuration and force the case of variable names to conform to the case of the entry within the symbol table entry. String comparisons are case sensitive by default, but can be made case insensitive if so desired.
The Visual Basic compiler is shared with other Visual Studio languages (C, C++), but restrictions in the IDE do not allow the creation of some targets (Windows model DLL's) and threading models.
[edit]
Characteristics present in Visual Basic
Visual Basic has the following traits which differ from C-derived languages:
Boolean constant True has numeric value −1.[3] This is because the Boolean data type is stored as a 16-bit signed integer. In this construct −1 evaluates to 16 binary 1s (the Boolean value True), and 0 as 16 0s (the Boolean value False). This is apparent when performing a Not operation on a 16 bit signed integer value 0 which will return the integer value −1, in other words True = Not False. This inherent functionality becomes especially useful when performing logical operations on the individual bits of an integer such as And, Or, Xor and Not.[4] This definition of True is also consistent with BASIC since the early 1970s Microsoft BASIC implementation and is also related to the characteristics of microprocessor instructions at the time.
Logical and bitwise operators are unified. This is unlike all the C-derived languages (such as Java or Perl), which have separate logical and bitwise operators. This again is a traditional feature of BASIC.
Variable array base. Arrays are declared by specifying the upper and lower bounds in a way similar to Pascal and Fortran. It is also possible to use the Option Base statement to set the default lower bound. Use of the Option Base statement can lead to confusion when reading Visual Basic code and is best avoided by always explicitly specifying the lower bound of the array. This lower bound is not limited to 0 or 1, because it can also be set by declaration. In this way, both the lower and upper bounds are programmable. In more subscript-limited languages, the lower bound of the array is not variable. This uncommon trait does exist in Visual Basic .NET but not in VBScript.
OPTION BASE was introduced by ANSI, with the standard for ANSI Minimal BASIC in the late 1970s.
Relatively strong integration with the Windows operating system and the Component Object Model.
Banker's rounding as the default behavior when converting real numbers to integers with the Round function.
Integers are automatically promoted to reals in expressions involving the normal division operator (/) so that division of an odd integer by an even integer produces the intuitively correct result. There is a specific integer divide operator (\) which does truncate.
By default, if a variable has not been declared or if no type declaration character is specified, the variable is of type Variant. However this can be changed with Deftype statements such as DefInt, DefBool, DefVar, DefObj, DefStr. There are 12 Deftype statements in total offered by Visual Basic 6.0. The default type may be overridden for a specific declaration by using a special suffix character on the variable name (# for Double, ! for Single, & for Long, % for Integer, $ for String, and @ for Currency) or using the key phrase As (type). VB can also be set in a mode that only explicitly declared variables can be used with the command Option Explicit.
[edit]
Evolution of Visual Basic
VB 1.0 was introduced in 1991. The drag and drop design for creating the user interface is derived from a prototype form generator developed by Alan Cooper and his company called Tripod. Microsoft contracted with Cooper and his associates to develop Tripod into a programmable form system for Windows 3.0, under the code name Ruby (no relation to the Ruby programming language).
Tripod did not include a programming language at all. Microsoft decided to combine Ruby with the Basic language to create Visual Basic.
The Ruby interface generator provided the "visual" part of Visual Basic and this was combined with the "EB" Embedded BASIC engine designed for Microsoft's abandoned "Omega" database system. The ability to load dynamic link libraries containing additional controls (then called "gizmos") which later became the VBX interface were added to the product at the request of Bill Gates[5].
[edit]
Timeline of Visual Basic (VB1 to VB6)
Project 'Thunder' was initiated
Visual Basic 1.0 (May 1991) was released for Windows at the Comdex/Windows World trade show in Atlanta, Georgia.
Visual Basic for MS-DOS
Visual Basic 1.0 for DOS was released in September 1992. The language itself was not quite compatible with Visual Basic for Windows, as it was actually the next version of Microsoft's DOS-based BASIC compilers, QuickBASIC and BASIC Professional Development System. The interface used the "COW" (Character Oriented Windows) interface, using extended ASCII characters to simulate the appearance of a GUI.
Visual Basic 2.0 was released in November 1992. The programming environment was easier to use, and its speed was improved. Notably, forms became instantiable objects, thus laying the foundational concepts of class modules as were later offered in VB4.
Visual Basic 3.0 was released in the summer of 1993 and came in Standard and Professional versions. VB3 included version 1.1 of the Microsoft Jet Database Engine that could read and write Jet (or Access) 1.x databases.
Visual Basic 4.0 (August 1995) was the first version that could create 32-bit as well as 16-bit Windows programs. It also introduced the ability to write non-GUI classes in Visual Basic. Incompatibilities between different releases of VB4 caused installation and operation problems.
With version 5.0 (February 1997), Microsoft released Visual Basic exclusively for 32-bit versions of Windows. Programmers who preferred to write 16-bit programs were able to import programs written in Visual Basic 4.0 to Visual Basic 5.0, and Visual Basic 5.0 programs can easily be converted with Visual Basic 4.0. Visual Basic 5.0 also introduced the ability to create custom user controls, as well as the ability to compile to native Windows executable code, speeding up calculation-intensive code execution.
Visual Basic 6.0 (Mid 1998) improved in a number of areas [6] including the ability to create web-based applications. VB6 has entered Microsoft's "non-supported phase" as of March 2008.
Mainstream Support for Microsoft Visual Basic 6.0 ended on March 31, 2005. Extended support ended in March 2008.[7] In response, the Visual Basic user community expressed its grave concern and lobbied users to sign a petition to keep the product alive.[8] Microsoft has so far refused to change their position on the matter. Ironically, around this time, it was exposed that Microsoft's new anti-spyware offering, Microsoft AntiSpyware (part of the GIANT Company Software purchase), was coded in Visual Basic 6.0.[9] Windows Defender Beta 2 was rewritten as C++/CLI code.[10]
Microsoft has developed derivatives of Visual Basic for use in scripting. Visual Basic itself is derived heavily from BASIC, and subsequently has been replaced with a .NET platform version.
Some of the derived languages are:
Visual Basic for Applications (VBA) is included in many Microsoft applications (Microsoft Office), and also in many third-party products like AutoCAD, WordPerfect Office 2002 and ArcGIS. There are small inconsistencies in the way VBA is implemented in different applications, but it is largely the same language as VB6 and uses the same runtime library.
VBScript is the default language for Active Server Pages. It can be used in Windows scripting and client-side web page scripting. Although it resembles VB in syntax, it is a separate language and it is executed by vbscript.dll as opposed to the VB runtime. ASP and VBScript should not be confused with ASP.NET which uses the .Net Framework for compiled web pages.
Visual Basic .NET is Microsoft's designated successor to Visual Basic 6.0, and is part of Microsoft's .NET platform. Visual Basic.Net compiles and runs using the .NET Framework. It is not backwards compatible with VB6. An automated conversion tool exists, but for many projects automated conversion is impossible.[11]
Earlier counterparts of Visual Basic (prior to version 5) compiled the code to P-Code or Pseudo code only. Visual Basic 5 and 6 are able to compile the code to either native or P-Code as the programmer chooses. The P-Code is interpreted by the language runtime, also known as virtual machine, implemented for benefits such as portability and small code. However, it usually slows down the execution by adding an additional layer of interpretation of code by the runtime although small amounts of code and algorithms can be constructed to run faster than the compiled native code. Visual Basic applications require Microsoft Visual Basic runtime MSVBVMxx.DLL, where xx is the relevant version number, either 50 or 60. MSVBVM60.dll comes as standard with Windows in all editions after Windows 98 while MSVBVM50.dll comes with all editions after Windows 95. A Windows 95 machine would however require inclusion with the installer of whichever dll was needed by the program.
Here are some examples of the language:
Program to display a pop-up message box with the words "Hello World" on it:
Private Sub Form_Load()
MsgBox "Hello World"
End Sub
Program to display an input box:
Sub Main()
Dim a As String
a = InputBox("Enter your name:")
MsgBox a
End Sub
Running Another Application Using Visual Basic:
Private Sub Run_Notepad()
Shell "notepad.exe", vbMinimizedFocus
'opens notepad
End Sub
Printing multiplication table of 5 on form:
Private Sub PrintMul_Click()
Dim I As Integer
For I = 1 To 10
Print 5; " x "; I; " = "; 5 * I
Next I
End Sub
Displaying all prime numbers below 1,000,000:
Private Sub DisplayPrimeNumbers()
Dim Num As Long
Dim NN As Long
Dim IsPrime As Boolean
For Num = 2 To 1000000
IsPrime = True
For NN = 2 To Int(Num / 2)
If Num Mod NN = 0 Then
IsPrime = False
Exit For
End If
Next
If IsPrime Then
MsgBox CStr(Num) + " is a prime number!"
End If
Next
End Sub
Source:http://en.wikipedia.org/wiki/Visual_Basic

